In the face of evolving threats, cybersecurity is increasingly becoming embedded in the wider enterprise risk management framework, with a renewed focus on maintaining a rich and accurate knowledge environment to assess changes in their operating state to strengthen data security, bolster governance and reporting functions, and enhance any crisis management response.
Hacks, leaks, theft, financial loss – these headlines have become commonplace. Financial institutions stand to lose tens of millions of dollars a year due to vulnerabilities in their enterprise. When coupled with the ever-increasing number of domestic and extra-territorial regulations, the way companies approach cybersecurity must shift.
When it comes to cyber threats (data theft, financial fraud, data destruction, operations disruption), banks face unique challenges at the intersection of cybercrime and financial crime. Regulatory breaches could result in financial penalties or prosecution. Worse yet, these challenges have only been amplified by the ongoing COVID-19 pandemic.
This new world requires a new narrative to approach cybersecurity, which treats cybersecurity as part of the greater enterprise risk management framework. Anchored by strong cyber risk management, organizations must implement crisis management, data security and protection, regulatory response, and governance and reporting functions to navigate this new world.
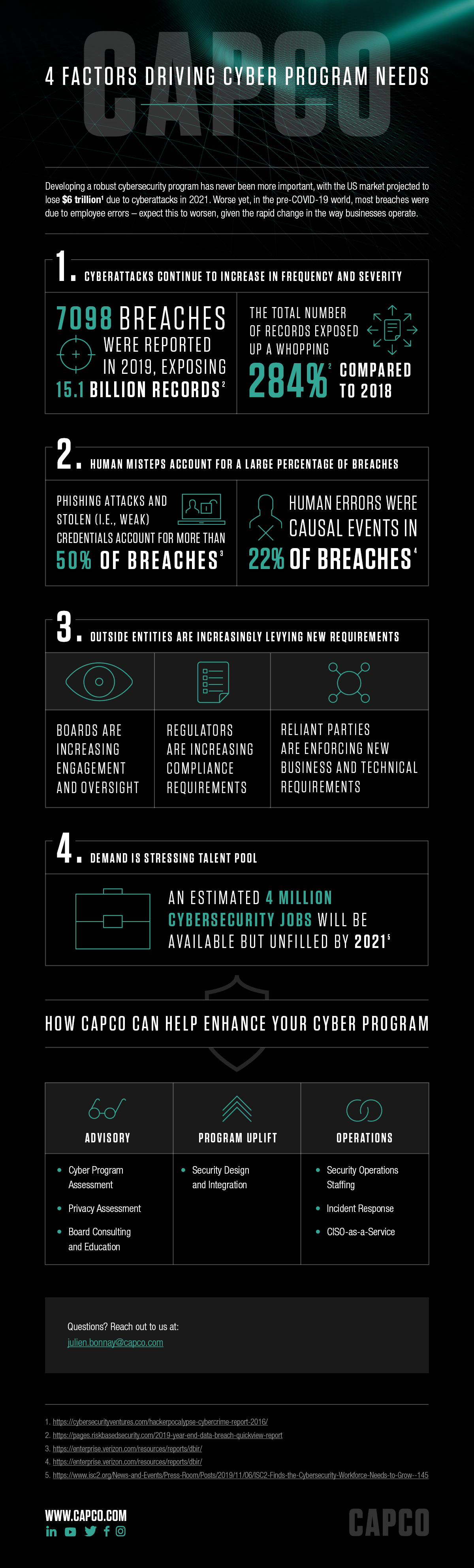
Capco brings together industry knowledge with expertise in risk management, cyber technology, and regulatory compliance to manage your cyber risk.
Capco’s offerings includes: